RabbitMQ Advanced Configurations
This section covers the following RabbitMQ advanced configurations:
RabbitMQ High Availability
Now, as RabbitMQ is being used by different Accops HyWorks Components, maintaining its high availability becomes very important, and it can be ensured in the following manner:
-
Using an external load balancer
-
Without a load balancer
Using an External Load Balancer
-
Two RabbitMQ servers will be installed behind a load balancer.
-
The Accops module that pushes messages to queues (publishers) will be configured to use a load balancer virtual address for the RabbitMQ servers. Publishers can send messages to any of the RabbitMQ servers.
-
Whereas the Accops modules, which consume messages (referred to as consumers), will be configured with both RabbitMQ server IPs. A message coming to any of the RabbitMQ servers via the load balancer will be picked up by the consumers.
Without a Load Balancer
-
Two RabbitMQ servers will be installed and configured without a load balancer.
-
All publisher components will have the host addresses of both RabbitMQs, and they will publish the message to only a single randomly selected server, which can then send the message to the first successful server.
-
Consumers are already listening on both servers and thus pick from any server on which the message has arrived.
Important
-
If the load balancer is not available in deployment: Both publisher and consumer components will be configured with the host addresses of both the RabbitMQ servers.
-
If the load balancer is available in deployment: The publisher will have the virtual address of the load balancer, and consumers will have the host addresses of both the RabbitMQ servers.
Configure RabbitMQ to use SSL
-
Login using the local administrator privileges.
-
Configure the RabbitMQ server using the RabbitMQ configuration steps.
-
Enable the management console using the following steps:
-
Open the Windows command prompt as an Administrator. Navigate to the RabbitMQ installation folder C:\Program Files\RabbitMQ Server\rabbitmq_server-3.12.2\sbin and enable the RabbitMQ management plugin by running the following command:
rabbitmq-plugins enable rabbitmq_management
-
Copy the following content into a file and save it as update_config.ps1.
``` $caCertFileName = "accopsmq_cert.pem" $serverCertFileName = "accopsmq_cert.pem" $serverPrivateKeyFileName = "accopsmq_key.pem" $rabbitmqVersion = "3.12.2" ## Variables that should not need modification $outPath = "$env:APPDATA\RabbitMQ" $utf8NoBomEncoding = New-Object System.Text.UTF8Encoding $False ## Write advanced.config file in UTF-8 encoding without BOM $advancedConfigText = @" [{rabbit, [ {ssl_options, [ {cacertfile, "$caCertFileName"}, {certfile, "$serverCertFileName"}, {keyfile, "$serverPrivateKeyFileName"} ]} ]}, {rabbitmq_management, [ {listener, [ {port, 15671}, {ssl, true}, {ssl_opts, [ {cacertfile, "$caCertFileName"}, {certfile, "$serverCertFileName"}, {keyfile, "$serverPrivateKeyFileName"} ]} ]} ]}]. "@ [System.IO.File]::WriteAllLines("$outPath\advanced.config", $advancedConfigText, $utf8NoBomEncoding) ## Write rabbitmq.conf in UTF-8 encoding without BOM $rabbitmqConfText = @" listeners.ssl.default = 5671 ssl_options.versions.1 = tlsv1.2 message_interceptors.incoming.set_header_timestamp.overwrite = true "@ [System.IO.File]::WriteAllLines("$outPath\rabbitmq.conf", $rabbitmqConfText, $utf8NoBomEncoding) ## Restart RabbitMQ Service Restart-Service -Name RabbitMQ ```
-
-
Copy the accopsmq_cert.pem and accopsmq_key.pem to %APPDATA%\RabbitMQ folder.
-
Open PowerShell as an administrator and navigate to the folder where the file created in the previous step is saved.
-
Run the file created in step 4 in PowerShell using the following command:
.\update_config.ps1 -
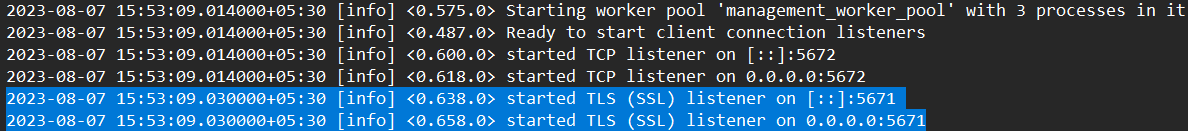
Ensure all the logs are seen, similar to the ones shown in the image below in the RabbitMQ logs located at %APPDATA%\RabbitMQ\log to ensure that RabbitMQ has started listening on the configured SSL port 5671.
-
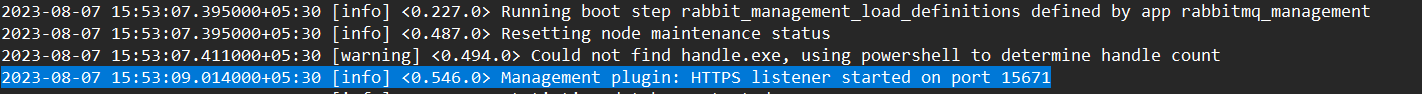
Also, make sure that all the logs are similar to the one in the image below in the RabbitMQ logs located at %APPDATA%\RabbitMQ\log to ensure that the RabbitMQ management console is also configured on SSL.
-
On the controller machine, navigate to https://localhost:15671 to access the RabbitMQ management console.
-
Allow inbound connection to port 5671 in the Windows firewall.
Steps to generate certificates required for RabbitMQ SSL configuration
Here, OpenSSL is used to generate certificates. Windows systems generally do not have OpenSSL installed. One option for running OpenSSL is to use Git Bash, which can be downloaded from here.
The following commands can be used to generate a private key and certificate, which will be used in the next section to configure SSL for RabbitMQ.
-
Command to generate a private Key:
-
Windows
winpty OpenSSL ecparam -out accopsmq_key.pem -name prime256v1 -genkey- LinuxOpenSSL ecparam -out accopsmq_key.pem -name prime256v1 -genkey
Note
In the above commands, the ECC curve "prime256v1" has been chosen since it was found to be available on the machines that we tested. Some details of choosing the curve "prime256v1" are mentioned here.
-
In case the private key and certificate generated do not work for you, you may check with one of the curves listed in the output of the command below.
OpenSSL ecparam -list_curves
-
-
Command to generate a certificate
-
Windows
winpty OpenSSL req -new -key accopsmq_key.pem -x509 -nodes -days 365 -out accopsmq_cert.pem -
Linux
OpenSSL req -new -key accopsmq_key.pem -x509 -nodes -days 365 -out accopsmq_cert.pem
-
Change the default RabbitMQ Port
-
Controller: Update the port in MMC > Advanced Config with Key[DVM Agent Queue Port].
-
HyWorks VM Scale Booster: Update the port [key: RabbitMQ > Port] in the config file:
-
Filename: appsettings.json
-
Path: C:\Program Files (x86)\Accops\HyWorks VM Scale Booster
-
-
Update the RabbitMQ port in the config file:
-
Path: C:\Users\Administrator\AppData\Roaming\RabbitMQ
-
File name: rabbitmq.config.example
-
Changes:
-
Existing string: %% {tcp_listeners, [5672]},
-
Updated string: {tcp_listeners, [5673]}
-
Please note that the comma is removed from the end.
-
Save the file and rename it to rabbitmq.config.
-
-
To reinstall RabbitMQ:
``` cd C:\\Program Files\\RabbitMQ Server\\rabbitmq_server-3.7.17\\sbin rabbitmqctl.bat stop rabbitmq-service.bat remove rabbitmq-service.bat install rabbitmq-service.bat start ```
-
Upgrade from the older to the newer RabbitMQ version
-
Login using the local administrator privileges.
-
Uninstall existing Erlang and RabbitMQ from the system.
-
Go to the path: C:\Users\{username}\AppData\Roaming and delete the RabbitMQ folder from it.
-
Here, the username is the user who has installed RabbitMQ.
-
If you are unable to delete the RabbitMQ folder and encounter exceptions, please restart the system and try deleting it afterward.
-
-
Delete the Erlang cookies from the following locations. There will be a file called .erlang.cookie that needs to be deleted from these paths:
-
C:\Users\{Username}
-
C:\Windows\System32\config\systemprofile
-
-
Download and install the supported Erlang OTP as a local administrator.
-
Download and install a supported RabbitMQ as a local administrator.